 How can a company you probably have never heard of position themselves to be managing mobile devices all over the globe? Only through the power of creating a network of partners, such as T-Mobile, Vodafone, BT, and Capgemini that places you smack in the middle of it all. That is exactly what Alex Bausch, CEO of VeliQ, set out to do and succeeded. I had the pleasure of meeting Alex at SAPPHIRE NOW and recently caught up with him for further details and insights.
How can a company you probably have never heard of position themselves to be managing mobile devices all over the globe? Only through the power of creating a network of partners, such as T-Mobile, Vodafone, BT, and Capgemini that places you smack in the middle of it all. That is exactly what Alex Bausch, CEO of VeliQ, set out to do and succeeded. I had the pleasure of meeting Alex at SAPPHIRE NOW and recently caught up with him for further details and insights.
VeliQ, the makers of MobiDM, started out in 2006 under the name of VeiligMobiel. Their first product secured Windows mobile smartphones for government agencies. But as the smartphone market evolved, so too did the product and the company. First, Bausch realized that the company’s name was too much of a mouthful for anyone outside of Holland to pronounce, so it was changed to VeliQ. Second, the product evolved into MobiDM, a cloud-based SaaS offering of what Bausch calls a “managed mobility ecosystem.”
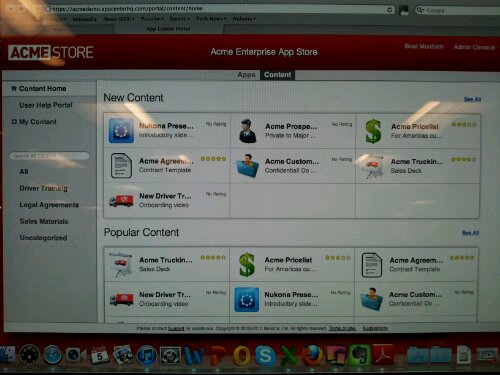
MobiDM provides a middleware solution around three main areas; Mobile Device Management, Security, and Application Management. When developing the product, Bausch looked at the existing MDM solutions available and decided to build MobiDM leveraging Afaria. “MobiDM is the mobile management middleware with the Afaria engine underneath,” Bausch noted. In 2008 they signed an OEM agreement with Afaria and haven’t looked back since.
Bausch believes that the service should be incredibly easy to use and sees that as a distinct advantage. He says comparatively “Afaria is a Boeing 747 with 500 levers, which you need a license and training for. MobiDM is like flying with JetBlue; come along for the ride and we’ll take care of everything.” Bausch believes that there is a time and a place for a more complex solution, but that MobiDM’s approach to simplicity is appealing to a large audience.
Bausch reaches that audience through lots of partnerships. In fact, the product is sold exclusively through partners. Bausch recalled that, “Because we were in Holland, there was lots of fragmentation to deal with. So we decided to sell exclusively through partners.” MobiDM has about 50 partners worldwide, made up of mostly telecom companies. Chances are you have never seen the MobiDM brand. That’s because partners such as Vodafone, T-Mobile, Sybase, and T-Systems all re-brand MobiDM’s service. “Our product is used under their own brand. That is the difference between us and a company like Airwatch; Airwatch sells direct.”
Through leveraging partnerships, MobiDM’s growth ramped up quickly. As Bausch put it, “We never sold MDM as a point solution; we sold the product as part of a mobile subscription. In year one we were up to 22,000 subscribers.” Their success doesn’t seem to show any signs of slowing either, as they signed 9 new partnerships in Q1 of this year. “The market is accelerating, that is why we believe in partnering and the ecosystem.”
With this kind of success, there have been other larger organizations that have tried to copy their offering. These solutions have since folded, while MobiDM continues today. “We have a different approach. We are successful because we have focus. We focused on usability, services andscalability.” As far as future competition, Bausch thinks that, “The threat is that there is so much money being thrown at [mobility management]. It creates a distortion field.”
So what does the future hold for Bausch and MobiDM? They recently released MobiDM Mobile Integrated Cloud. This allows subscribers to the service to integrate with Jamcracker, Single Sign On providers for AD integration, and line-of-business apps for SAP. Bausch wants to only continue this partnering/ecosystem line of thinking. “The trend that we see is, it’s not MDM that is important, but rather it is the whole ecosystem.” With the strong partnerships in place, and more to come, it is hard to see how they can lose.
 Mobile Device Management by MobiDM provides a Software as a Service (SaaS) solution which makes smartphone and PDA management easy. All your mobile devices can be installed, managed and secured from a single central portal, regardless of the type of device, network or operating system, leaving users free to go about their business with no loss of productivity.
Mobile Device Management by MobiDM provides a Software as a Service (SaaS) solution which makes smartphone and PDA management easy. All your mobile devices can be installed, managed and secured from a single central portal, regardless of the type of device, network or operating system, leaving users free to go about their business with no loss of productivity.




 I want to give you a sneak peek into my conversation with
I want to give you a sneak peek into my conversation with 